The Axios Supply Chain Attack
Why This Was a Wake-Up Call — And What It Tells Us About Trust in Modern Software
The software supply chain has evolved into the primary theater of operation for advanced persistent threats, and last night, we witnessed a nuclear-grade bomb drop on the JavaScript ecosystem. Let us not undersell the magnitude of what happened on March 31, 2026. The internet is essentially a vast, interconnected dependency hell. The people building the digital infrastructure we rely on everyday use tools built by other people, which are in turn built by others, and sometimes maintained by one random, thankless volunteer. This entire house of cards is ripe for compromise. That fragility was fully exposed when the Axios npm package was hijacked.
Axios is a promise-based HTTP client downloaded over 100 million times a week. It is a foundational element of modern web architecture, present in roughly 80 percent of cloud and code environments. When an asset of this scale is compromised, it is not just a localized breach. It is a systemic shockwave. This article provides a comprehensive post-mortem of the Axios supply chain compromise, an analysis of the evolving threat landscape fueled by automated development practices, and a deep dive into how Red Hat’s Architecture of Trust provides the necessary fortifications to secure the modern software factory.
The Anatomy of a Nuclear-Grade Compromise
The breach of Axios was not a spontaneous crime of opportunity. It was a pre-staged, multi-phase operation orchestrated by UNC1069, a threat actor with a well-documented North Korea nexus. Their objective was not to deface websites or steal end-user data directly. They were hunting developers. By poisoning a foundational package, the attackers aimed to infiltrate the systems of the engineers building the internet, pilfering SSH keys, cloud provider secrets, and environment tokens to facilitate massive financial theft and leapfrog into production environments.
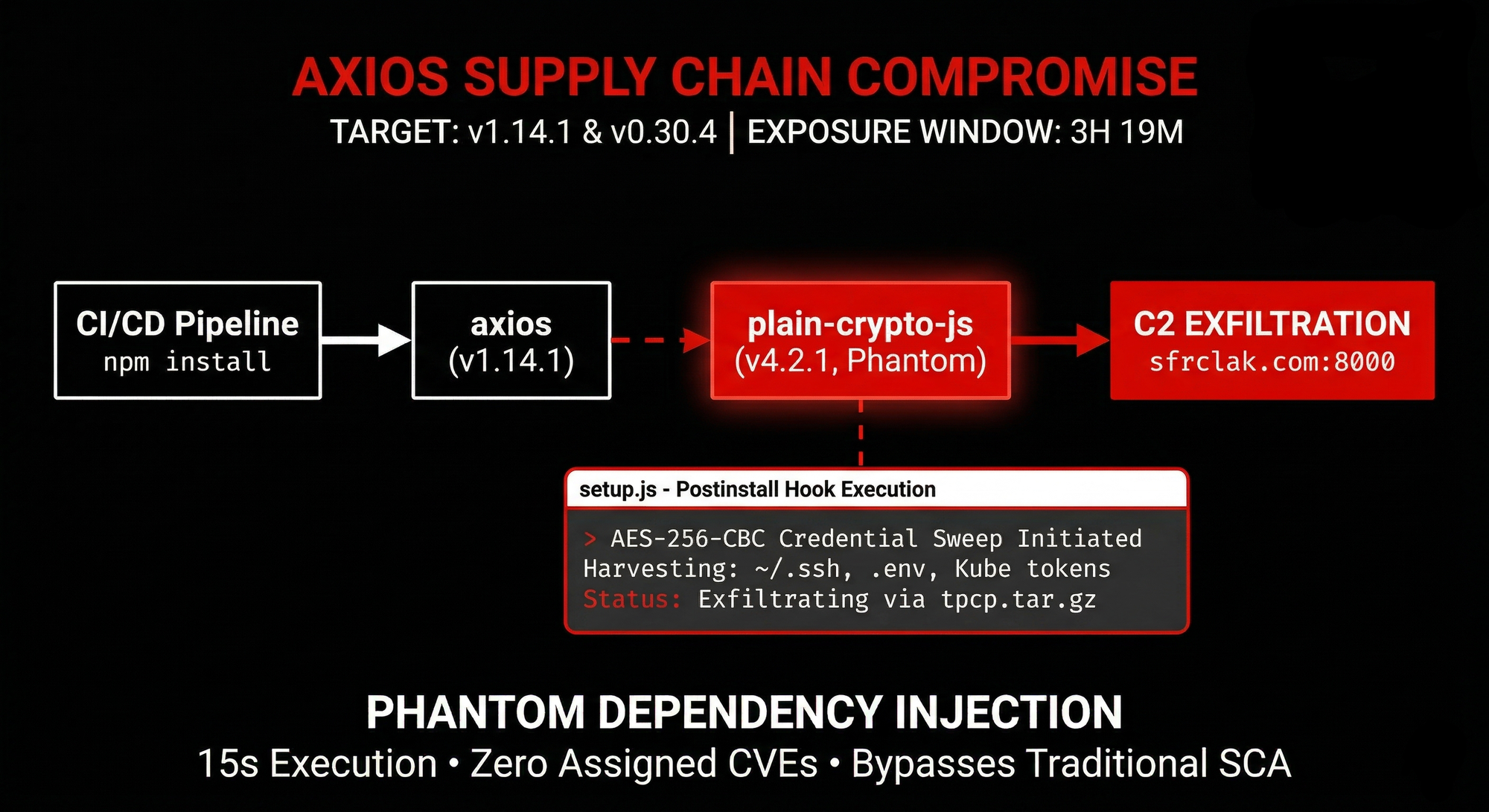
The operation prioritized stealth and forensic evasion. The attackers understood the npm registry metadata heuristics perfectly. Before launching the actual payload, they seeded a benign decoy package named plain-crypto-js at version 4.2.0. This established a clean publication history, ensuring that the automated security scanners would not immediately flag the subsequent malicious update as a high-risk debut.
Hours later, the attackers compromised the npm credentials of Jason Saayman, the lead maintainer of Axios. Whether this was achieved through session token theft, a targeted phishing campaign, or an older compromised credential remains a subject of investigation. However, the result was catastrophic. The attackers changed the account recovery email to an anonymous ProtonMail address, locking the legitimate maintainer out of his own project.
Using these hijacked credentials, the threat actors bypassed the official GitHub Actions continuous integration pipelines and mandatory code reviews. They published malicious versions of Axios directly through the npm command-line interface. By pushing version 1.14.1 for modern applications and 0.30.4 for legacy enterprise systems within a tight 39-minute window, they ensured maximum distribution. Anyone running a standard installation command during that period was pulling malware directly into their environment.
The Phantom Dependency and the Vibe Coder Threat
The infection vector relied on a structural weakness in the npm ecosystem known as the postinstall lifecycle hook. The malicious versions of Axios were functionally identical to their legitimate predecessors, save for a single added line in the package.json file requesting the plain-crypto-js package at version 4.2.1. This library was never actually imported into the Axios source code. It functioned entirely as a phantom dependency, existing solely to trigger its own setup script during the installation process.
When a developer or an automated system resolved the dependency tree, the registry automatically executed the setup script. This script employed a highly sophisticated two-layer obfuscation scheme to hide a Remote Access Trojan known as WAVESHAPER.V2. The decryption key was dynamically calculated using a non-linear index formula. Upon successful decryption, the dropper identified the host platform and pulled down a specialized payload. macOS users received a Mach-O C++ binary capable of ad-hoc codesigning to bypass Gatekeeper. Windows environments were infected via heavily obfuscated PowerShell scripts that established persistence through the system registry. Linux environments were hit with transient native Python backdoors.
The malware then aggressively scrubbed its own tracks. It deleted the original setup script, removed the poisoned package.json, and swapped in a clean manifest. A security team inspecting the directory post-installation would find what appeared to be a perfectly legitimate software package.
This invisible execution highlights a terrifying new risk vector in the era of artificial intelligence: the "vibe coder." Modern development heavily relies on AI agents and coding assistants like OpenClaw or local models like Hermes. Developers often prompt these agents to build entire applications and walk away, granting the AI full system access to install dependencies and execute code. If a vibe coder asks an AI to build a weather application, the AI will likely pull in Axios to handle the web requests. If the developer is not auditing the code or the dependency tree, they are blindly trusting an automated system to pull unverified third-party code into a privileged environment. This blind trust is exactly what state-sponsored actors are weaponizing.
The Systemic Failure of Implicit Trust
The Axios incident exposed the profound market failure of open-source sustainability and the inherent danger of implicit trust. The JavaScript ecosystem operates on an philosophy where applications rely on thousands of tiny, transitive dependencies. An organization might not directly install Axios, but their backend framework or third-party security tool almost certainly does.
The core vulnerability is the trust boundary between a maintainer's credentials and the registry pipeline. Most package managers treat a valid authentication token as the ultimate authority. If an account is taken over, no amount of upstream code review matters. Furthermore, automated development tools implicitly trust that the binary artifact downloaded from the registry matches the source code stored on GitHub. The manual publish bypass used in the Axios attack proved that these two entities can diverge completely.
While registries have attempted to harden their systems by deprecating classic tokens and enforcing session-based authentication, manual bypasses remain possible. The industry is rapidly realizing that relying on the heroic efforts of burned-out, unfunded maintainers to secure global infrastructure is an unsustainable strategy.
The Architecture of Trust: Red Hat OpenShift Ecosystem
The transition from opportunistic malware to industrialized supply chain warfare necessitates a fundamental architectural shift. Organizations can no longer accept the frictionless, default-allow consumption of open-source code. They must adopt a default-deny security architecture. Red Hat’s comprehensive suite of technologies, encompassing the Trusted Software Supply Chain, OpenShift Advanced Cluster Security, and Red Hat Quay, provides a holistic solution designed precisely to map against these modern vulnerabilities.
The philosophy of the Red Hat security portfolio is built upon curating trusted content, safeguarding the build system, and enforcing strict runtime protections. This multi-layered defense ensures that integrity is maintained from the integrated development environment all the way to the production workload.
I have written a comprehensive article on the topic of software supply chain few years ago, showcasing Red Hat's capability to address challenges like the example with Axios. You can read the article following this link https://www.vitalijneverkevic.com/red-hats-trusted-software-supply-chain/
Curating Content and Securing the Build Pipeline
The first defense against a poisoned package is ensuring that the raw materials of software are verified before they ever enter the pipeline. Red Hat Trusted Profile Analyzer acts as the centralized system of record for this verification. It ingests Software Bills of Materials in standard formats like CycloneDX to map out the exact dependency tree of an application. By pairing this with Vulnerability Exploitability Exchange data, security teams can pinpoint exactly which dependencies carry risk and whether those vulnerabilities are actually exploitable in their specific configuration.
To address the threat of compromised build environments, Red Hat utilizes Konflux and the Trusted Application Pipeline. These tools democratize the secure software factory, automating the generation of artifacts that comply with Supply-chain Levels for Software Artifacts Level 3 standards. Konflux emphasizes hermetic builds, which are isolated from the internet to prevent the exact type of cross-build contamination and dependency hijacking seen in the Axios attack. Source.
A critical component of this process is the Red Hat Trusted Artifact Signer. Cryptographic signing is the only verifiable way to link an artifact to its creator. TAS utilizes keyless signing technology through OpenID Connect identities and a transparency log called Rekor. This completely eliminates the need for developers to manage long-lived private keys, which are frequent targets for credential theft. If the Axios organization had strictly enforced verifiable provenance attestations through a system like TAS, the malicious packages published directly via the command line would have lacked the necessary cryptographic signatures and been automatically rejected by any secure deployment pipeline.
Precision Static Analysis with Quay and Clair
Securing the dependency stack requires an environment where software can be analyzed without the risk of triggering malicious lifecycle hooks. Red Hat Quay serves as the secure container registry, deeply integrated with the Clair static analysis engine.
The Axios malware relied on the automated execution of a postinstall script. Clair bypasses this trap entirely. It is a static scanner that inspects container images layer-by-layer without executing the underlying code. The Clair Indexer fetches image layers and parses manifest files, identifying all installed software and package manager metadata. The Matcher then cross-references this inventory against a massive, continuously updated database of vulnerabilities.
By performing this analysis statically, Clair can detect known malicious packages or vulnerable dependencies buried deep within the transitive tree before the container is ever instantiated. Source1. Source2.
For organizations struggling with the sheer volume of vulnerabilities in the Python and JavaScript ecosystems, Red Hat introduced Project Hummingbird and Trusted Libraries. Project Hummingbird delivers minimal base images that target a near-zero vulnerability standard. Trusted Libraries extend this concept to the application level. Instead of pulling binaries blindly from public registries, developers can configure their package managers to use Red Hat’s curated index. These packages are built from source within Red Hat’s hardened infrastructure, effectively blocking typosquatting, dependency confusion, and credential hijacking attacks at the source. Source1. Source2.
Advanced Cluster Security: The Runtime Guardian
Even with rigorous static analysis and cryptographic provenance, highly sophisticated malware can sometimes slip through, executing only under specific runtime conditions. This is where OpenShift Advanced Cluster Security (ACS) acts as the ultimate workload gatekeeper.
ACS integrates natively with the OpenShift via Operator framework to enforce security policies and monitor behavior from build to runtime. The ACS Admission Controller intercepts requests to the OpenShift API server, ensuring that only images meeting strict security criteria are allowed to run. If an image lacks a valid signature from the Trusted Artifact Signer, or if Clair flags it as containing a critical vulnerability, the Admission Controller blocks the deployment entirely.
Once a workload is running, ACS provides continuous behavioral analysis. The WAVESHAPER RAT used in the Axios attack relied on establishing a command and control connection, beaconing out to an external server every 60 seconds. ACS continuously monitors network traffic across all clusters and pods. It visualizes allowed versus active traffic, allowing administrators to implement strict network segmentation. By enforcing a Zero Trust network policy, ACS ensures that a compromised pod cannot communicate with unauthorized external servers or move laterally within the network.
Furthermore, ACS monitors system-level events for anomalous activity. If a supposedly benign web container suddenly attempts to execute arbitrary shell commands, access sensitive configuration paths, or modify the system registry, ACS detects this behavioral signature. The system can be configured to take automated remediation actions, such as instantly killing the compromised pod or dynamically updating network policies to quarantine the threat.
The Mandate for Resilience
The compromise of Axios marks the definitive end of the frictionless publishing era. The assumption that open-source software is inherently safe because it is publicly visible has been proven false by state-sponsored actors capable of highly sophisticated, pre-staged subversion. The speed of software development must now be balanced against the rigorous security standards required to survive in an environment of pervasive supply chain warfare.
Organizations must treat their development environments with the same level of security scrutiny as their production servers. Implementing update delays, enforcing lockfiles, and disabling automated lifecycle scripts are critical immediate steps. However, long-term resilience requires a systemic overhaul.
By integrating Red Hat’s Architecture of Trust, organizations can map these severe supply chain challenges directly to actionable, automated solutions. From the continuous verification of dependencies in the IDE, to the hermetic, cryptographically signed build processes of Konflux, to the unwavering runtime vigilance of Advanced Cluster Security, Red Hat provides the holistic framework necessary to build and maintain trust. In an interconnected digital economy where a single compromised dependency can trigger a global fallout, adopting a default-deny, secure-by-default architecture is no longer just a best practice. It is the ultimate mandate for organizational survival.